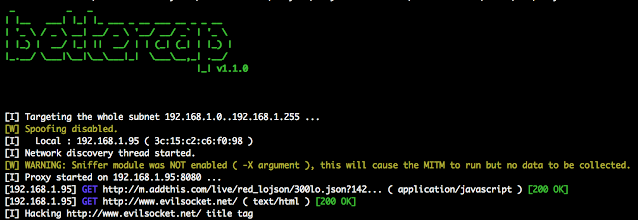
Bettercap is a complete, modular, portable and easily extensible MITM tool and framework with every kind of diagnostic and offensive feature you could need in order to perform a man in the middle attack
What is Bettercap?
How It is better than Ettercap.
- Ettercap was a great tool, but it made its time.
- We've found ettercap filters to simple not work in many cases as they are outdated and also haven't been maintained as there aren't as many low-level C programmers interested in maintaining it.
- ettercap is freaking unstable on big networks ... If you've tried to use ettercap's host discovery feature on any large network you'll see it simply can't scale well.
- yeah you can see connections and raw pcap stuff, nice toy, but as a professional researcher, I want to see only relevant stuff.
- unless you're a C/C++ developer, you can't easily extend ettercap or make your own module.
Installation
Stable Release ( GEM )
gem install bettercap
Development Release
git clone https://github.com/evilsocket/bettercap cd bettercap gem build bettercap.gemspec sudo gem install bettercap*.gem
Dependencies
sudo apt-get install ruby-dev libpcap-devHow is it possible?
Features of Bettercap.
Dynamic Host Discovery + ARP Spoofing
You can target the whole network or a single known address. The ARP spoofing capabilities and multiple hosts discovery agents will make rest of the work easier.Credentials Sniffer.
It has got a built-in credentials sniffer which can gather from the network the following information:
- URLs being visited.
- HTTPS host being visited.
- HTTP POSTed data.
- HTTP Basic and Digest authentication.
- FTP credentials.
- IRC credentials.
- POP, IMAP and SMTP credentials.
- NTLMv1/v2 ( HTTP, SMB, LDAP, etc ) credentials.
Modular Transparent Proxy
Built in HTTP/HTTPS/MDNS/MySQL Server
Other Modules
BetterCAP is a powerful network analysis and penetration testing tool that provides several modules for various tasks. These modules are designed to be highly customizable and extensible, allowing users to tailor the tool to their specific needs. Here's a high-level overview of some of the most important modules available in BetterCAP:
arp.spoof - This module performs ARP spoofing attacks to intercept network traffic between two hosts. This module is useful for performing man-in-the-middle attacks and for testing the security of web applications.
dns.spoof - This module performs DNS spoofing attacks to intercept DNS requests and redirect them to a different IP address. This module is useful for testing the security of web applications and for identifying vulnerabilities such as cross-site scripting (XSS) and SQL injection.
proxy.http - This module intercepts HTTP traffic and allows users to modify and inspect the traffic in real-time. This module is useful for analyzing web traffic and for testing the security of web applications.
proxy.https - This module intercepts HTTPS traffic and allows users to inspect and modify the encrypted traffic. This module is useful for testing the security of SSL/TLS implementations and for identifying vulnerabilities such as weak cipher suites.
arp.spoof.plugin - This module provides a framework for creating custom plugins to extend the capabilities of the ARP spoofing module. This module is highly extensible and allows users to create custom plugins for specific tasks.
net.sniffer - This module captures network traffic and allows users to analyze the traffic in real-time. This module is useful for network reconnaissance and for identifying suspicious network activity.
net.recon - This module performs network reconnaissance and mapping to identify hosts and services on a network. This module is useful for identifying vulnerabilities and for preparing for more advanced penetration testing.
net.probe - This module performs active network scanning to identify hosts and services on a network. This module is useful for identifying open ports and for preparing for more advanced penetration testing. For a complete list of modules, refer Official Bettercap website









COMMENTS