This article discusses Cloudflare's successful mitigation of a record-breaking DDoS attack, which targeted one of its customers.
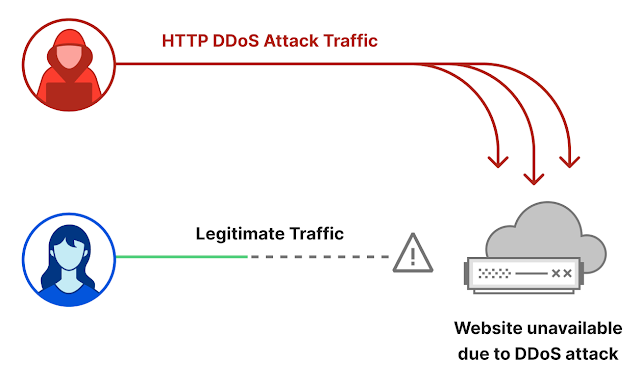
A DDoS attack is a type of cyberattack that aims to take down a website or service by overwhelming it with a massive amount of traffic. This traffic is generated by a network of compromised devices, known as a botnet. The botnet can be controlled remotely by the attackers, who use it to send a large number of requests to the target server, making it impossible for legitimate users to access the service.
Record Breaking DDoS volume
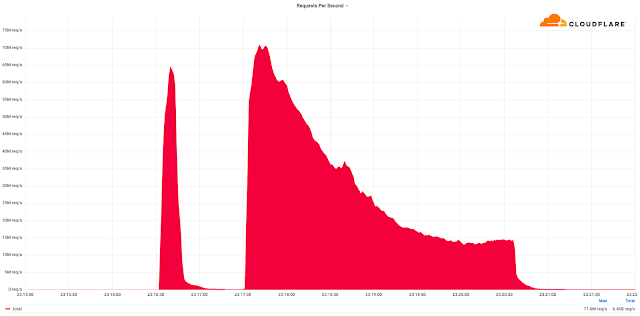
Cloudflare, the popular content delivery network, recently mitigated a record-breaking Distributed Denial of Service (DDoS) attack, which targeted one of its customers. The attack generated a massive 17.2 million queries per second (QPS), which translates to 71.8 billion requests per minute. This attack was the largest ever reported, and it surpassed the previous record of 15.3 million QPS, set in 2018.
DDoS attack leveraging CLDAP vulnerability
The attack on Cloudflare was different from traditional DDoS attacks, as it involved a new type of protocol called Connectionless Lightweight Directory Access Protocol (CLDAP). This protocol is commonly used in Microsoft Active Directory servers, which are used to manage users and computers on a network.
The attackers exploited a vulnerability in the CLDAP protocol, which allowed them to amplify the amount of traffic being sent to the target server. This type of attack is known as an amplification attack, and it allows attackers to generate a massive amount of traffic using a small amount of resources.
Mitigation Techniques
To mitigate the attack, Cloudflare used a combination of techniques, including rate-limiting, filtering, and scrubbing. Rate-limiting involves limiting the number of requests that can be sent to the target server, while filtering involves blocking traffic from known bad sources. Scrubbing involves analyzing incoming traffic and removing any malicious traffic.
Cloudflare also used a technique called Anycast, which involves using multiple servers in different locations to handle incoming traffic. Anycast allows Cloudflare to distribute the incoming traffic across its network, making it easier to handle large amounts of traffic.
Despite the massive scale of the attack, Cloudflare was able to mitigate it within a few minutes, thanks to its advanced DDoS mitigation capabilities. The company has invested heavily in DDoS mitigation technology and has developed a range of tools and techniques to handle different types of attacks.
In addition to DDoS mitigation, Cloudflare offers a range of security services, including a web application firewall, bot management, and security analytics. These services are designed to help organizations protect their websites and applications from a wide range of cyber threats.
Conclusion
This attack on Cloudflare highlights the importance of having robust cybersecurity measures in place. Organizations need to be aware of the latest threats and vulnerabilities and invest in advanced security technologies to protect their networks and systems. In the case of DDoS attacks, it is important to have a DDoS mitigation strategy in place, which includes the use of tools and techniques such as rate-limiting, filtering, and scrubbing. It is also important to have an incident response plan in place, which outlines the steps to be taken in the event of a cyberattack.






COMMENTS